August 2025 Privacy Pulse: Cybersecurity Risks & The mePrism Defense
1. Minnesota lawmaker shooting—data brokers played a role
In June, Minnesota was shaken by violence that revealed how dangerous open access to personal data has become.
Vance Boelter allegedly assassinated State Rep. Melissa Hortman and her husband, and shot State Sen. John Hoffman and his wife. Court records show Boelter used people-search websites (data brokers) to track home addresses. He even kept a notebook listing 11 data broker sites and dozens of potential targets (Politico).
Lawmakers, including Senators Amy Klobuchar and Ron Wyden, said the attack highlights how easily accessible personal information can enable violence and called for tighter regulation of data brokers. This case underscores that data exposure is not just a digital risk—it is a real-world safety issue.
2. Data brokers hiding opt-out pages from search
New reporting shows that many data brokers are actively trying to make it harder for people to exercise their rights.
A joint WIRED/CalMatters investigation found at least 35 major data brokers—including IQVIA, Comscore, and Telesign—using technical tricks to hide their “delete my data” pages from Google and Bing (WIRED).
Senator Maggie Hassan demanded answers by September 3, calling this tactic a “dark pattern” designed to keep personal data flowing and make opting out nearly impossible (WIRED). If brokers are deliberately burying opt-outs, consumers and organizations need trusted partners to ensure rights are exercised effectively.
3. ShinyHunters Salesforce and enterprise breaches
The cybercrime group ShinyHunters has escalated its attacks on corporate systems, targeting CRM and SaaS platforms.
Google: The company itself admitted falling victim to a Salesforce-related breach via social engineering (ITPro).
Workday and Chanel confirmed similar breaches, with attackers stealing employee and customer contact data.
Allianz Life: The worst case so far—2.8 million sensitive records leaked, including SSNs, tax IDs, addresses, and birthdates (TechRadar).
ShinyHunters thrives on data broker-style information—employee names, emails, and phone numbers—that fuels phishing, fraud, and deeper breaches.
4. Healthcare: cyber incidents on the rise
The healthcare sector continues to face record-breaking attacks, with millions of patients and providers exposed.
DaVita ransomware impacted 2.7 million people, encrypting parts of its lab database across ~3,000 clinics (Reuters).
1.2 million unsecured devices leaked sensitive scans and images (MRI, X-rays, bloodwork) worldwide (TechRadar).
Texas Digestive Specialists reported a ransomware incident affecting 41,500 patients (MySA).
Episource (Optum-owned) suffered a breach hitting 5.4 million people (Tom’s Guide).
HHS reports 307 healthcare breaches already in 2025, on pace to exceed last year’s record (WSJ). The trend is clear: patient safety and trust are being undermined by a combination of ransomware, poor data governance, and weak device security.
Why This Matters
Physical safety risks: Data broker exposure has already been linked to stalking, harassment, and violence.
Cyber risks: Criminal groups like ShinyHunters are using public and brokered data to compromise enterprise systems.
Deceptive practices: Brokers are burying opt-outs, betting you won’t find them.
Organizational risk: Employee contact details online make it easy for attackers to impersonate staff or target executives.
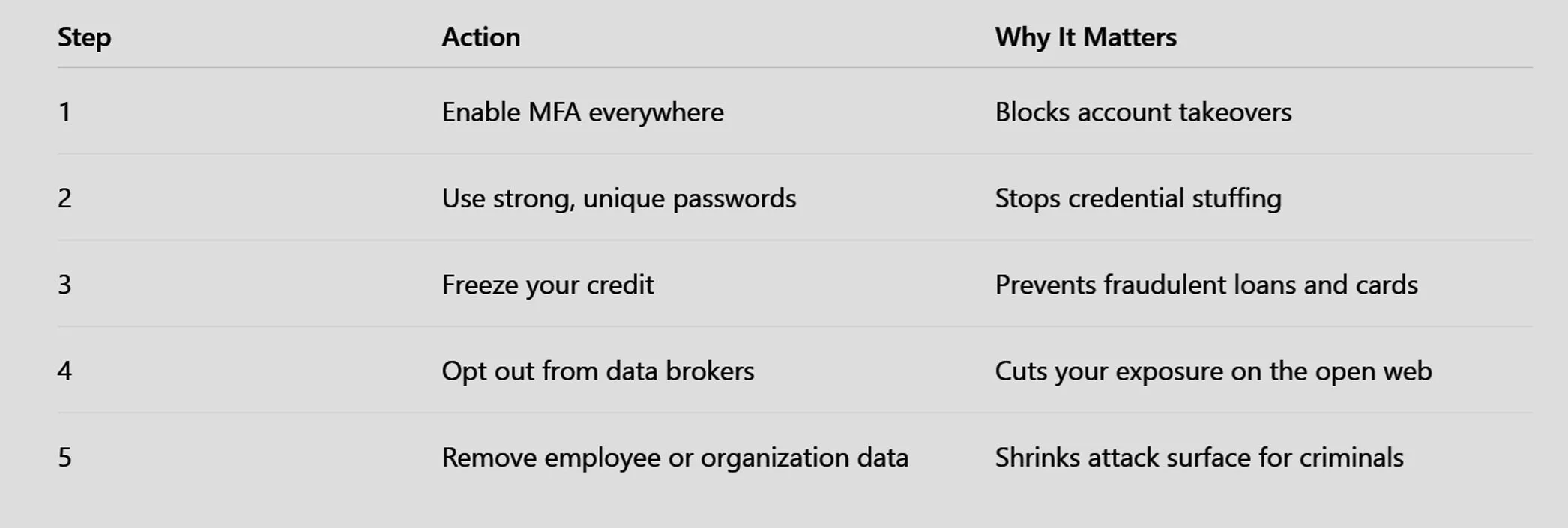
What You Can Do Now: The mePrism Defense
Personal Protections
Enable multi-factor authentication (MFA) on all critical accounts (email, bank, mobile).
Use strong, unique passwords—password managers make this simple.
Freeze your credit reports at Experian, TransUnion, and Equifax.
Be cautious with calls or emails—verify before sharing information or clicking links.
Organizational Protections
Remove employee and organizational data from data brokers. This reduces the fuel attackers use for social engineering. Priwall automates this process, escalating legal requests and continuously monitoring for re-exposure.
Harden SaaS and CRM platforms: Enforce least-privilege access and use phishing-resistant MFA.
Secure medical and IoT devices: Change defaults, segment networks, and actively monitor for leaks.
Take Back Control
Data brokers profit by selling your personal and organizational data. Criminals—from stalkers to ransomware gangs—are using that same data to target people, businesses, and institutions.
You can’t prevent every attack, but you can shrink your exposure:
Lock down your accounts.
Freeze your credit.
Step behind the cloak: Remove your information—and your employees’ information—from the open web.
The ShinyHunters & Social Engineering Defense Checklist
In a world where groups like ShinyHunters use brokered data to infiltrate enterprise SaaS and CRM platforms, traditional security is no longer enough.
1. Strong Authentication
Phishing-Resistant MFA: Transition to FIDO2, hardware keys, or passkeys.
Retire Legacy MFA: Phase out SMS and voice-based MFA, which are easily intercepted.
Contextual Re-auth: Require re-authentication for high-risk or sensitive administrative actions.
2. Access Controls & Monitoring
Zero Trust / Least Privilege: Apply strict access limits across the entire organization.
Just-in-Time (JIT) Access: Use temporary admin permissions that expire after the task is complete.
Geographical Monitoring: Alert on logins from unknown devices or inconsistent geographies.
3. Employee Resilience & Awareness
Attacker Playbooks: Train staff on real-world tactics, such as fake IT support calls and sophisticated phishing scripts.
Simulation Testing: Run regular phishing and vishing (voice phishing) simulations.
Frictionless Reporting: Provide a "one-click" method for employees to report suspicious activity.
4. SaaS & CRM Hardening
App Whitelisting: Block unapproved third-party tools and "shadow IT."
Permission Audits: Regularly review and prune third-party app permissions.
Export Alerts: Set automated triggers for unusually large data exports or bulk activity.
5. Incident Response Ready
SaaS-Specific Playbooks: Maintain a dedicated response plan for SaaS credential compromise.
Log Review: Consistently collect and review SaaS logs for anomalies.
Tabletop Exercises: Run live simulations of a breach to test team response times.
6. External Exposure Reduction (The Priwall Core)
Automated Data Scrubbing: Use Priwall to remove employee data from data brokers, stripping attackers of their primary research tools.
Minimize Public Footprints: Limit the amount of company hierarchy and contact detail available on public-facing websites.
Continuous Scanning: Perform ongoing monitoring for re-emerging data as brokers attempt to re-populate their databases.
Take Back Control
Data brokers profit by selling your personal and organizational data. Criminals—from stalkers to ransomware gangs—are using that same data to target people, businesses, and institutions.
You can’t prevent every attack, but you can shrink your exposure:
Lock down your accounts with phishing-resistant MFA.
Freeze your credit at the major bureaus.
Step behind the cloak: Remove your information—and your employees’ information—from the open web.
Ready to step behind the block the source?
At Priwall, we help you take back control. Our service scans the web for exposed personal information and automates the removal process.
Click here to create your Free Basic account.Explore more from Our Team
Browse more posts written by our team to help you stay in control.
Be Part of the Conversation